
Many companies doing business in regulatory environments treat compliance like another obstacle to success. However, successful companies have proven that to meet regulatory compliance is to embrace a tool that can give them a competitive advantage.
According to IBM’s latest study on cloud transformation, 64 percent of C-suite executives at regulated companies say that ensuring compliance with regulatory requirements is one of the most important challenges in their company.
Instead of resisting regulations, smart companies embrace them and leverage their weight to find success.
Read more on how companies are adapting to changing regulations: Data Collection Ethics: Bridging the Trust Gap
Executives must meet regulatory compliance
Without having a clear understanding of what is required by law, senior level executives can find themselves in hot water. C-level executives are specifically responsible for:
- Remaining knowledgeable on relevant regulations for their company/industry
- Taking action to make pertinent areas of business remain compliant
- Documenting action taken to achieve or maintain compliance
- Furnishing proof of compliance in audit procedures
Compliance is a murky territory, as some regulations apply broadly, while others are industry-specific.
Compliance for all US companies
Some regulations apply to all businesses in the US. Those pertaining to accounting, payment information, and environmental impact are just a few examples.
Accounting
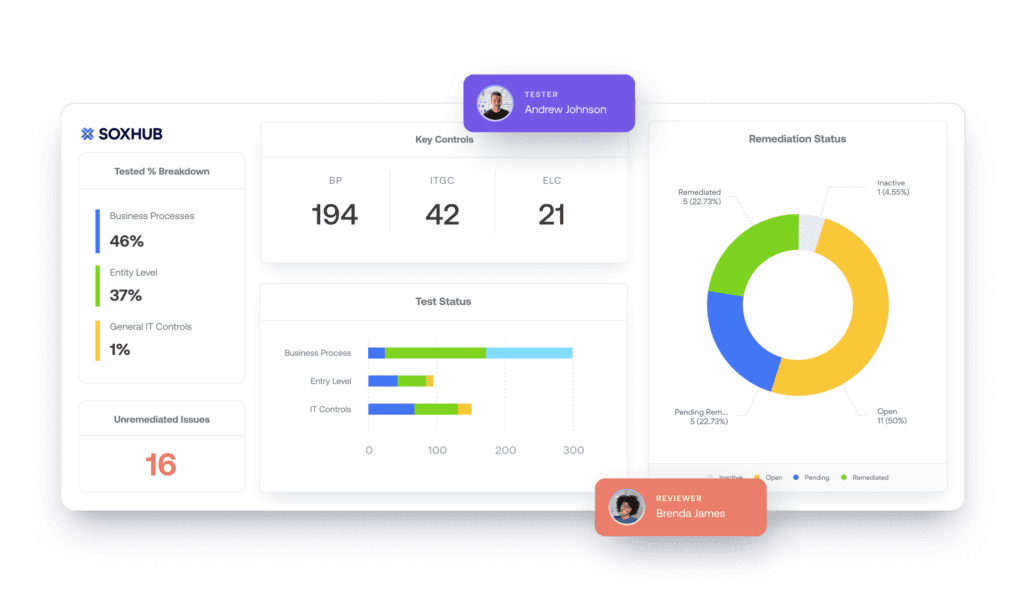
The Sarbanes-Oxley (SOX) Act requires US businesses to maintain proper accounting practices for fraud prevention and for tax purposes, including filing taxes, receiving tax cuts, and other tax-related procedures. AuditBoard is an enterprise platform that includes SOX regulation management
B2C payment information
Given the ubiquity of consumer credit card and debit card purchases, virtually all B2C businesses must also comply with the Payment Card Industry Data Security Standard (PCI-DSS).
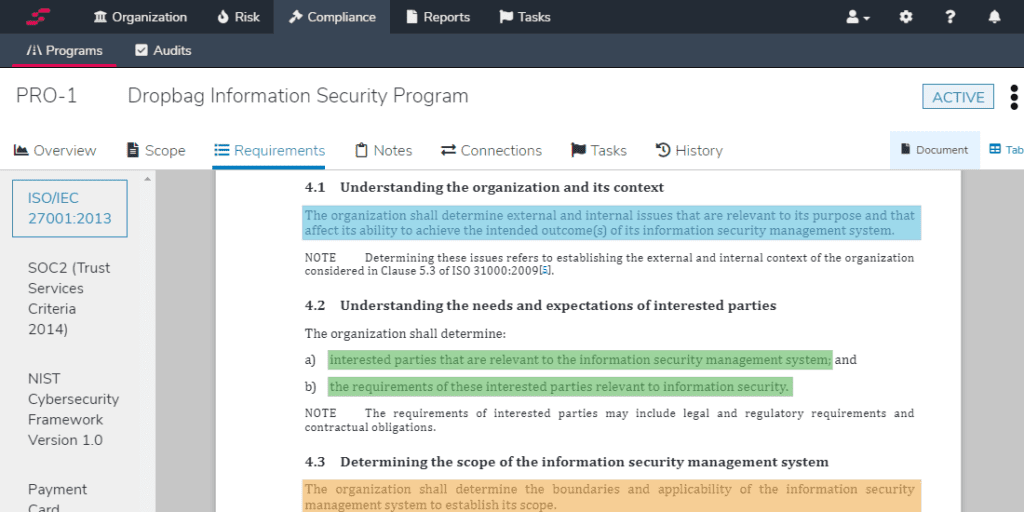
This standard stipulates how businesses store, process, and transmit consumer financial data. StandardFusion is a governance, risk, and compliance software solution that helps businesses with PCI-DSS compliance and other regulatory frameworks.
Environmental impact
The inception of the Environmental Protection Agency (EPA) and a series of industry-specific legislative acts led to regulations that aim to reduce public and private organizations’ environmental footprint. Affected sectors include agriculture, automotive, construction, electric utilities, oil and gas, and transportation.
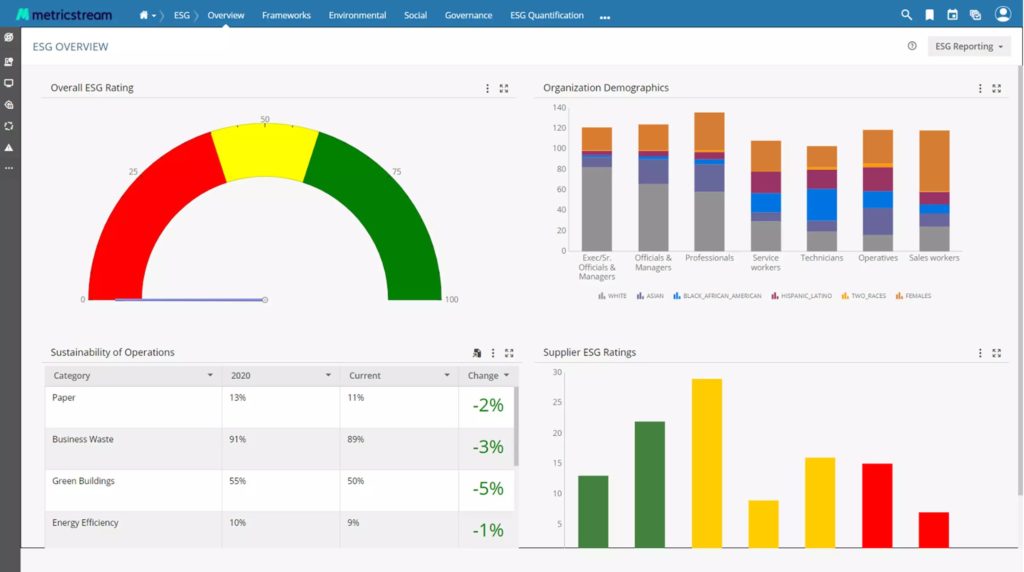
MetricStream has a product dedicated to environmental, social, governance, risk, and compliance (ESGRC). Its ESGRC provides real-time visibility into how your organization is performing against environmental metrics.
International companies
US-based companies that collect, manage, and store data on citizens of the European Union are subject to General Data Protection Regulation (GDPR). GDPR ensures consumer data protection and privacy.
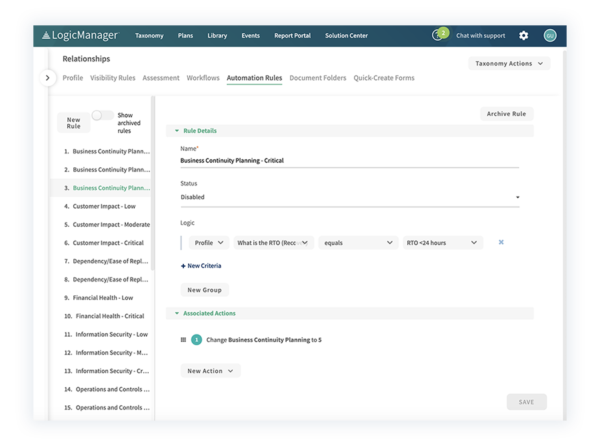
LogicManager is enterprise risk management software that assists international companies with remaining GDPR compliant by identifying compliance gaps, assessing risks, helping create effective policy, and more.
Compliance looks different based on industry
While some compliance measures apply to most or all US businesses, the degree and specifics of compliance often depend on the industry a business operates in.
Healthcare
In the healthcare industry, companies must maintain compliance with the Health Insurance Portability and Accountability Act (HIPAA). Clinical practices, insurance companies, and other entities that operate in healthcare must protect patients’ privacy by securing their health records.
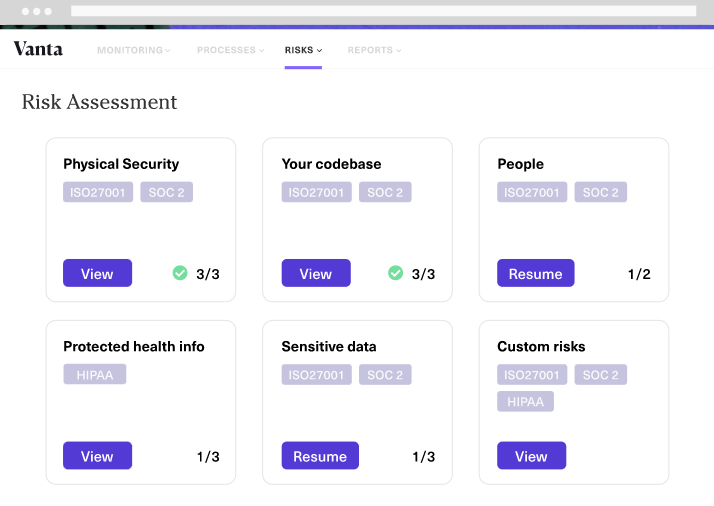
Vanta supports businesses in a variety of compliance frameworks, including HIPAA. It features automated compliance tools that scan, verify, and secure your IT systems and processes to protect patients’ medical information.
In addition, the ISO 13485 guidelines help medical device companies demonstrate that their quality management system consistently meets applicable regulatory requirements.
In order to do so, companies must document changes in a range of items:
- Identification numbers
- Descriptions of names
- Diagrams
- Process charts
- Technical specifications
- Quality plans
- Check lists
- Manufacturing specifications
- Standard procedures
- Computer files
- Bills of materials
- Assembly plans
- Test protocols
- Approved list of suppliers
A single slip in the documentation process incurs a penalty. Arena is a cloud-based quality management system that helps your medical-device businesses adhere to ISO guidelines and those of other regulatory bodies by helping with document management.
Tech
The National Institute of Standards and Technology (NIST) is a non-regulatory agency that strives to elevate technology standards and best practices in the US. NIST has issued a set of baseline metrics and practices for the tech industry in terms of security, Internet-of-Things (IoT) devices, hiring, and other technology-related matters.
Check Point provides a unified cybersecurity platform that follows NIST guidelines, using automatic testing and reporting to identify compliance gaps.
Compliance is everyone’s business
There is a widespread misunderstanding that compliance is simply the responsibility of the quality department or legal counsel in any given organization, but that isn’t the case.
In order to ensure corporate compliance with FDA and other global regulations and standards, it’s imperative that every department works together to communicate what’s at stake in meeting regulations:
- Reputation
- Investigation
- Fines
- Legal fees
Beyond communication, organizations must take action to train employees and enforce measures that apply to the organization to ensure compliance. Periodic reminders and ongoing training are effective ways to keep each part of the organization aligned with compliance.
To make a data-driven case for compliance, read more: What Is Predictive Analytics?
How to meet regulatory compliance
We’ve outlined some practices below to ensure your organization meets the regulatory standards.
Implement compliance software
Compliance means keeping up a certain quality standard in order to avoid product recalls or, worse, litigation. Quality and compliance systems are complex and often difficult to manage across an entire enterprise, particularly in highly regulated environments. Automating such processes with an electronic quality management system (eQMS), for example, benefits an organization in several ways:
- Boost efficiency
- Accelerate product delivery
- Enhance quality
- Maintain regulatory compliance
- Reduce costs
Organizations must not only ensure product quality, but also have insight into all quality processes. Software solutions that collect and report on quality KPIs help companies not only maintain a certain quality standard but also meet regulatory standards.
Incorporate a training software system
Training is a critical element of regulatory compliance. The most streamlined way for companies to manage training tasks and related compliance requirements is to provide employees with continuous training tools.
For example, a training software system is a critical regulatory requirement for the FDA and global regulatory inspectors. An automated training system reduces audit time and findings and decreases the risk of product recalls. Added benefits include improved product quality and safety, increased customer satisfaction, and FDA and ISO compliance.
Be prepared for a regulatory audit
Almost all types of businesses undergo an audit, so being prepared is critical to the success of a company. Regular audits are necessary to comply with regulations and ensure product safety and quality. To make it easier to ensure regulatory compliance, companies should implement an audit management software system that will facilitate all audit-related tasks and activities.
Without an effective audit reporting tool, like one from IBM OpenPages, Riskonnect, or SAI360, managers may find it problematic to generate accurate and timely reports for auditors, which could cause all kinds of issues down the road. Incorporating audit management software helps to provide analytics and reporting that enable management to receive real-time views of the audit process.
Read more: What Is a 3-2-1 Backup Strategy?
Make compliance a top priority
Compliance is no easy task, but it’s a worthwhile and necessary undertaking to ensure user privacy and safety, deliver a high-quality product or service, and boost your company’s reputation. Though compliance largely falls on C-level management, all levels of the organization must be committed to it as well.
A compliance software solution coordinates compliance measures across the enterprise and provides valuable insights into an organization’s quality processes. Compliance software automatically scans and reports on your current compliance status, identifies gaps, makes recommendations for improvement, maintains auditing documentation, and much more.