Can Two-Factor Authentication Fix Mobile Security?
 Can Two-Factor Authentication Fix Mobile Security?
Can Two-Factor Authentication Fix Mobile Security?
In an effort to combat mobile security concerns, IT decision-makers are turning to two-factor authentication as a service.
 Majority Restrict Mobile Access
Majority Restrict Mobile Access
92% of IT departments worldwide still restrict users from accessing sensitive corporate data and resources from mobile devices.
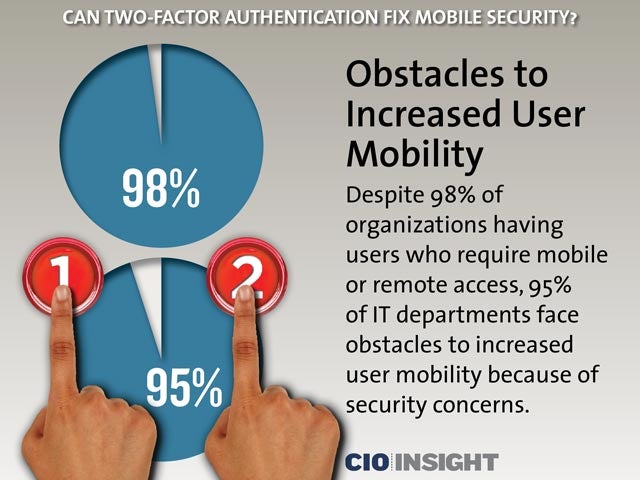 Obstacles to Increased User Mobility
Obstacles to Increased User Mobility
Despite 98% of organizations having users who require mobile or remote access, 95% of IT departments face obstacles to increased user mobility because of security concerns.
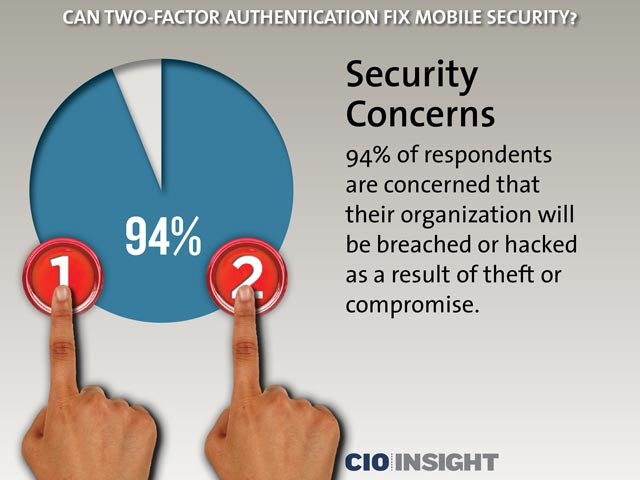 Security Concerns
Security Concerns
94% of respondents are concerned that their organization will be breached or hacked as a result of theft or compromise.
 Mobile Endpoints Add to Concern
Mobile Endpoints Add to Concern
The rise of mobile, which on average is two mobile endpoints per user and managing three sets of credentials per user, is exacerbating security concerns.
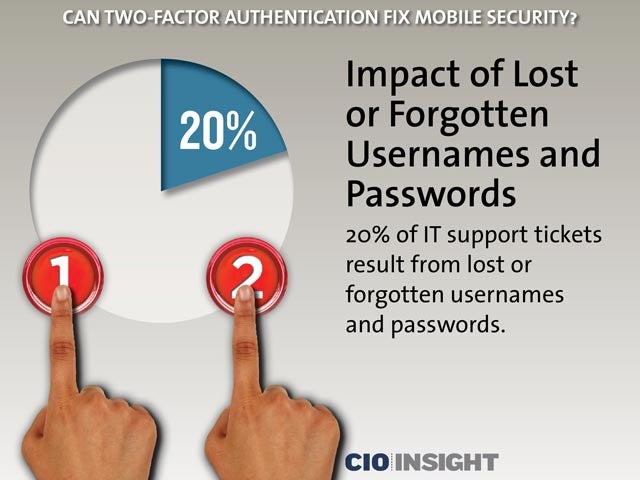 Impact of Lost or Forgotten Usernames and Passwords
Impact of Lost or Forgotten Usernames and Passwords
20% of IT support tickets result from lost or forgotten usernames and passwords.
 Overcoming the Mobile Security Challenge
Overcoming the Mobile Security Challenge
To overcome mobile security challenges, 86% of IT departments plan to implement two-factor authentication for access to cloud applications. 38% of users do so now and this is expected to rise to 51% in two years.
 Two-Factor Authentication Now
Two-Factor Authentication Now57% of respondents already use two-factor authentication to secure external users’ access.
 Top Three Apps Protected By Two-Factor Authentication
Top Three Apps Protected By Two-Factor Authentication
92% of respondents have at least one application protected by two factor authentication. The top three apps: cloud applications, web portals and VPNs.
 Rise of Authentication as a Service?
Rise of Authentication as a Service?
91% of respondents seek to solve the credential problem with two-factor authentication that is a cloud-based authentication as a service. 90% regard cloud delivery as a key consideration when choosing to buy such solutions.













