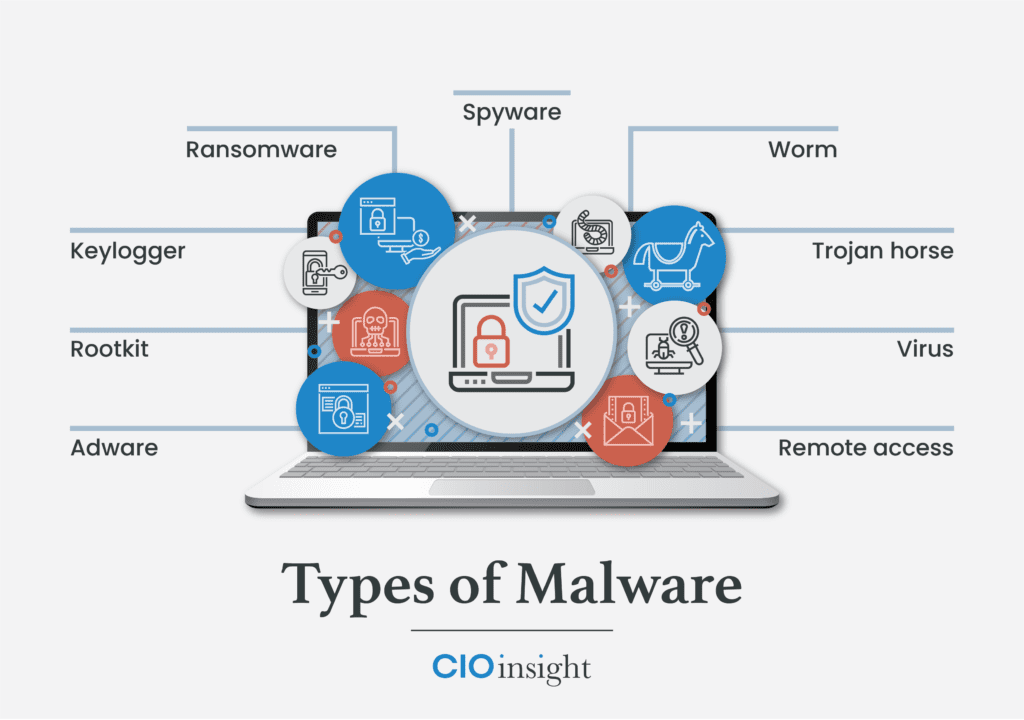
As a member of Senior IT, you want to select the best malware protection software for your organization. Whether it’s a zero-day exploit via adware, an attempted ransomware lockdown, or a trojan horse trying to run amok on your network, you want these malware bandits to be neutralized as fast as possible.
Time is of the essence to mitigate risk. The goal of malware protection tools is identifying suspicious files such as adware, keyloggers, spyware, trojan horses, worms, and viruses to quickly minimize potential damage to a business network’s devices. Malware is popular among cybercriminals and a constant threat, as it’s used to gain leverage over businesses for financial gain.
Table of Contents
- Malware Protection Software Comparison
- Best Malware Removal & Protection Software
- How Malware Protection Tools Work
- Malware Protection Software Features
- Select the Best Malware Protection Software for Your Business
Malware Protection Software Comparison
| Vendor | Cloud-Based Protection | VPN Service | Adware Protection | Compatibility with PC, Mac, Android & iOS | Business Size |
|---|---|---|---|---|---|
| Cisco Umbrella with Secure Endpoint | ✅ | ✅ | ✅ | ✅ | Midsize to Large |
| Avast CloudCare | ✅ | ✅ | ✅ | ✅ | Midsize to Large |
| AVG Antivirus Business Edition | ✅ | ✅ | ✅ | ❌ | Small to Midsize |
| ESET PROTECT | ✅ | ❌ | ❌ | ❌ | Small to Midsize |
| Bitdefender GravityZone | ✅ | ✅ | ❌ | ✅ | Small to Midsize |
| McAfee MVISION Cloud | ✅ | ✅ | ❌ | ✅ | Midsize to Large |
| Norton Small Business | ✅ | ✅ | ❌ | ✅ | Small |
Remote and hybrid work environments are more prevalent today than ever. The need to protect an organization’s endpoint devices from malware attacks is essential. The comparison chart above lists a few of the many cloud-based malware protection tools available; each can provide remote malware protection as if the laptop were physically connected to the business network. When compiling our list of the best malware protection software, we included solutions appropriate for small, midsize, and large businesses.
Any malware protection software that did not offer USB scanning or scheduled scanning was not considered for review. Remote work locations offer an increased potential to introduce malware via the USB port; therefore, scanning a USB connected device at any time is paramount to minimizing any possible malware attack. The malware vendors we selected are strong candidates for protecting your network, with slight variations in the services offered based on your individual needs.
Read more: VPNs, Zero Trust Network Access, and the Evolution of Secure Remote Work
Best Malware Removal & Protection Software
CISCO Umbrella
Cisco Umbrella protection starts with internet infrastructure devices, which are the network devices, web servers, internet servers, and transmission media to connect computers. Cisco Umbrella attempts to prevent any malware from penetrating the network at the frontline, internet infrastructure level using its interactive threat intelligence data.
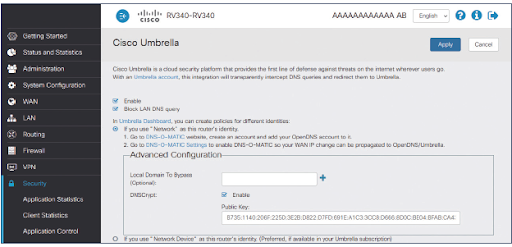
Combining Cisco Umbrella with Cisco Secure Endpoint makes it a comprehensive business malware protection package. Secure Endpoint adds another layer of protection, should the malware get to any endpoint device. Secure Endpoint provides malware protection to cell phones, tablets, desktops, and laptops connected to the business network or remotely through the cloud.
Endpoint protection continually communicates with the most updated intelligence to mitigate any potential malware threats on endpoint devices. This comprehensive malware protection bundle is designed for large organizations, but very capable of supporting the midsize and small organizations that can afford it.
Avast CloudCare
Avast CloudCare offers a total cloud-based malware protection package with a couple of additional features. Avast adds an additional level of encryption for passwords you want to protect, along with a WiFi inspection. That tool scans your computer to minimize the chances of malware infiltrating a computer or network.
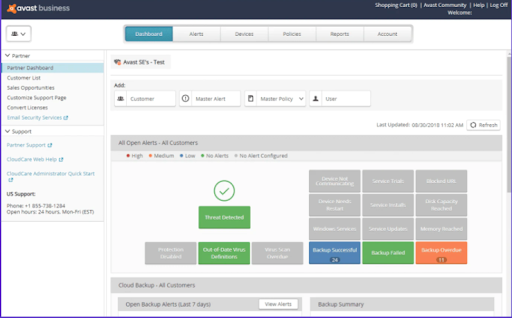
Avast advertises its product for small businesses with a hundred employees or less, but it also says its CloudCare solution can support up to a thousand devices globally. Avast’s key features are customizable data protection modules and an updated application control interface.
Avast uses a concept called behavior, web, and email, shields to protect businesses against suspicious requests or malicious emails. Also, Avast employs a data shredder that overwrites any deleted files — making it impossible for anyone to recover files in a data breach. SharePoint safeguarding is used to scan for malware on any uploads or downloads on business servers. Evaluators of the CloudCare solution liked the anti-spam capabilities for email, the WiFi inspector, and the ability to remove bad plugins.
AVG Antivirus Business Edition
A key feature of AVG is its built-in artificial intelligence (AI) that detects and prevents a malware outbreak to the network. AVG uses behavioral analysis with statistical testing to provide ransomware protection.
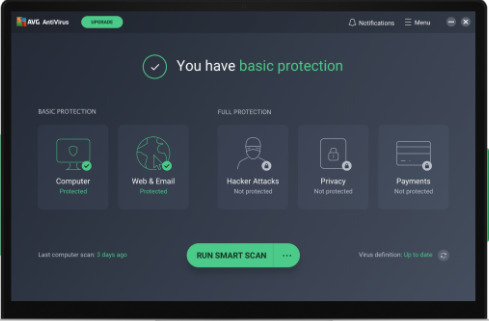
Another advertised feature of AVG is that this antivirus software provides identity protection. This product is designed for small businesses; it’s suitable for any small business that needs to protect clients’ personal information. The AVG cloud management console allows a business owner to remotely monitor threats, schedule scans or updates, and protect devices.
The ability to remotely manage devices is what evaluators liked most about AVG cloud solutions. The evaluators also complimented the safety rankings displayed for each web page opened.
ESET PROTECT
ESET provides malware protection services for small to midsize businesses. ESET addresses cybersecurity in a twofold process, offering cybersecurity training and a cloud-based malware protection solution. ESET recognizes that human error contributes to over 90% of malware breaches and thus offers extensive cybersecurity awareness online training.
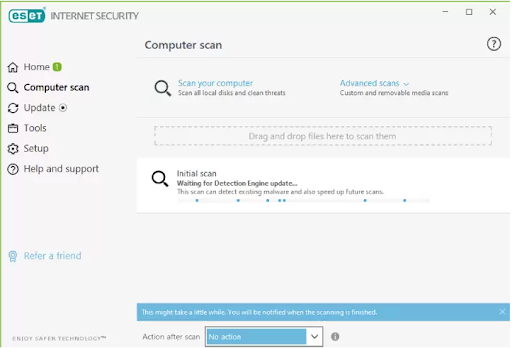
Senior IT management can invest $1,625 to train 100 employees on cybersecurity best practices. Combining the user training with an ESET cloud-based malware protection solution is a good starting point for a business looking to improve its cybersecurity posture.
Some cybersecurity experts describe ESET as good, but not a top-of-the line cybersecurity solution. ESET is known to provide reliable detection against malware, and it’s touted as being effective against zero-day attacks. ESET’s Host Intruder Prevention System (HIPS) module has shown to be very reliable at recognizing ransomware attacks and neutralizing them. Further, ESET’s user-friendly graphical user interface (GUI) makes it easy to use and set up.
Bitdefender GravityZone
Bitdefender is reviewed as one of the better malware protection solutions. This vendor’s package creates several layers of protection before malware can attack a computer or server. Bitdefender uses risk analytics to highlight a device’s vulnerability to malware. From this same risk management dashboard, a cyber-technician can make changes to configuration settings to reduce device vulnerabilities.
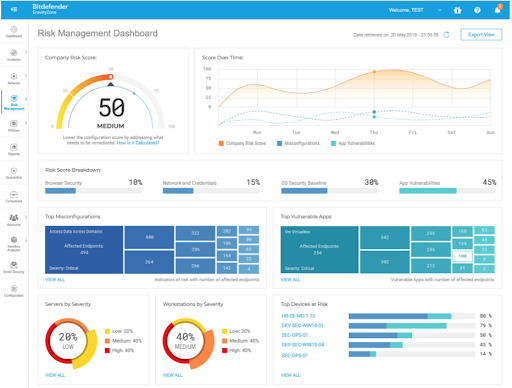
Bitdefender features advanced threat prevention that minimizes the need for manual intervention. The advanced threat security (ATS) module is an add-on that provides an additional method to discover hard-to-detect malware. ATS contains three sub-modules all designed to stop malware from fully executing:
- HyperDetect: Uses machine learning to stop malware attacks before execution
- Fileless Attack Defense: Inspects command code in memory, and prevents code from executing scripts using PowerShell or the Command prompt
- Sandbox Analyzer: Fully executes malware files to be used in identifying other similar malware files
Evaluators of Bitdefender GravityZone like the easy-to-use interface, and the ability to manage user access to web sites and applications.
McAfee MVISION Cloud
McAfee has expanded its services well beyond the typical antivirus software for home use. McAfee MVISION Cloud services allow a business to manage its cloud-based applications across multiple cloud computing services, such as Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
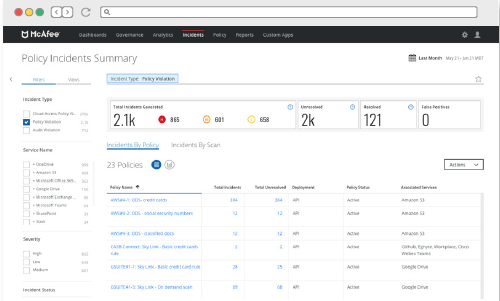
MVISION is a multi-cloud management solution that can enforce policies based on business content rules. Once MVISION is implemented, it can protect against any cloud threats across all cloud computing services. MVISION is omnipresent for a business network on any cloud computing service, with the ability to take control over data or cloud activity from any console.
MVISION can identify any potential insider threat through machine learning, as well as identifying suspicious user behavior. This McAfee product can identify inactive accounts or an account with elevated access that is not needed by the account holder. Based on behavior analysis, MVISION can identify malware and initiate on-demand scanning using real-time historical data to determine if the file is malware. McAfee’s MVISION has a plethora of state-of-the-art cloud options, making it very attractive for managing cloud-based business transactions.
Norton Small Business
Norton is a popular antivirus software package among consumers, but its business solution is also attractive. Norton Small Business reviews state it’s a very effective malware protection solution. For instance, Norton has a “find device” feature that can send alarms when a mobile phone or iPad is misplaced, pinpointing a user’s lost devices. With remote lock or wipe, Norton can prevent data on Android phones from being compromised.
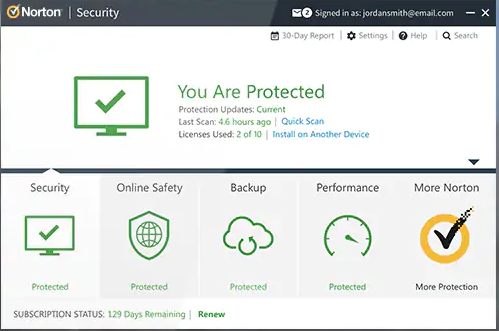
The Norton Small Business package can support up to 20 devices at a reasonable cost. Norton helps keep costs low for small businesses by prorating the price for any new devices added throughout the annual cycle. Norton’s web-based management portal allows you to see all registered devices and identify any devices at risk. The Norton Small Business solution had favorable features and positive feedback from evaluators.
How Do Malware Protection Tools Work?
To identify and remove malware, malware protection tools use three methods. First, Malware protection tools can use a definition file, known as a blacklist or malware signatures. The malware protection software then compares suspicious files against known operational behavior of files on the blacklist. It then flags the suspicious file for removal if the behaviors are the same. Antivirus also uses a similar signature-based detection to identify suspicious files.
The second malware protection methodology uses heuristics, or behavioral analysis, to identify suspicious files. A file can be identified as suspicious if it behaves in a manner that exhibits malware behavior, such as removing important files from a networked device. Anti-malware can isolate a file it has never seen before; conversely, antivirus software can never isolate a threat it has never before seen. The downside to heuristics is it can give false positives.
The last anti-malware method is called sandboxing, where a suspicious file is moved to a sandbox for further observation to determine if it’s malware.
Malware Protection Software Features
Good malware protection tools provide the following protections for business devices:
- Real-time malware protection: Any time a file is accessed, the file is scanned.
- Vulnerability protection profiles: Prevents malware from exploiting system vulnerabilities and gaining access to devices. It also protects against illegal code execution and buffer overflows.
- Scheduled scans: Flexibility to do impromptu scans helps mitigate potential zero-day attacks. Additional scanning options can be narrowing down to a specific file size, or excluding certain file extensions from being scanned.
- Protecting remote devices: The software can issue password change reminders, use data encryption, test security, and limit data access to essential personnel only.
- Anti-phishing protection: Software packages can contribute to employee education, as well as blocking suspicious emails and scanning email for any malicious content.
Select the Best Malware Protection Software for Your Business
As you can tell, many of the good malware protection tools provide similar functionality to protect the network and its devices. One easy selection criterion is determining the number of employees or devices requiring protection. Another is cost.
What is a business willing to pay for a good malware protection tool? Identify your cybersecurity requirement in its totality, and then Senior IT needs to invest the dollar amount needed to meet that defined requirement.
Read next: Top Cyber Security Threats to Organizations