Companies Grow More Vulnerable to Insider Threats
 Companies Grow More Vulnerable to Insider Threats
Companies Grow More Vulnerable to Insider Threats
Insider threats are increasing, privileged IT users and admins are the riskiest users, and monetizing sensitive data is the top reason for insider attacks.
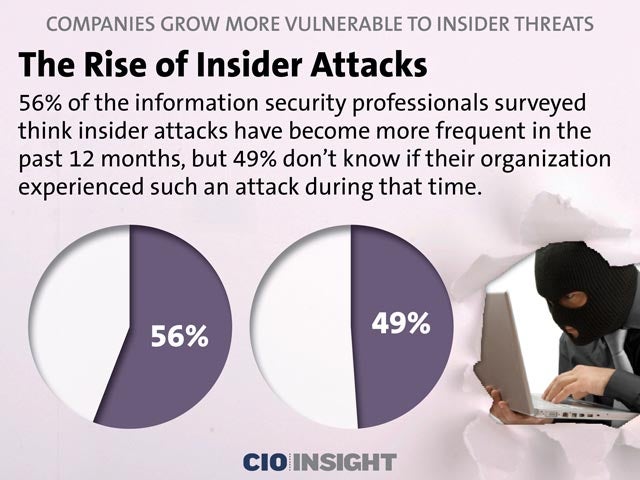 The Rise of Insider Attacks
The Rise of Insider Attacks
56% of the information security professionals surveyed think insider attacks have become more frequent in the past 12 months, but 49% don’t know if their organization experienced such an attack during that time.
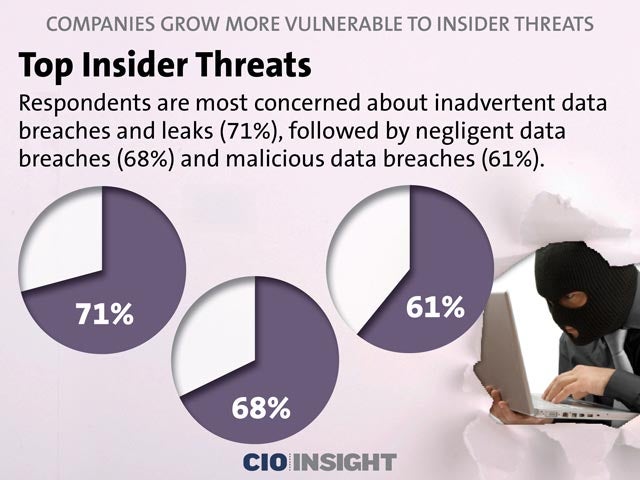 Top Insider Threats
Top Insider Threats
Respondents are most concerned about inadvertent data breaches and leaks (71%), followed by negligent data breaches (68%) and malicious data breaches (61%).
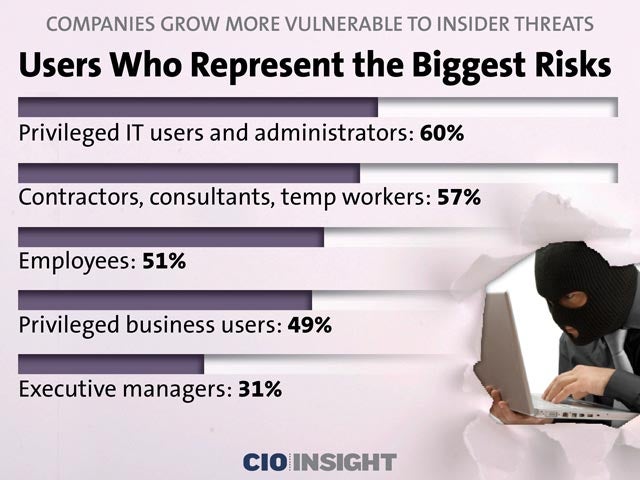 Users Who Represent the Biggest Risks
Users Who Represent the Biggest Risks
Privileged IT users and administrators: 60%,
Contractors, consultants, temp workers: 57%,
Employees: 51%,
Privileged business users: 49%,
Executive managers: 31%
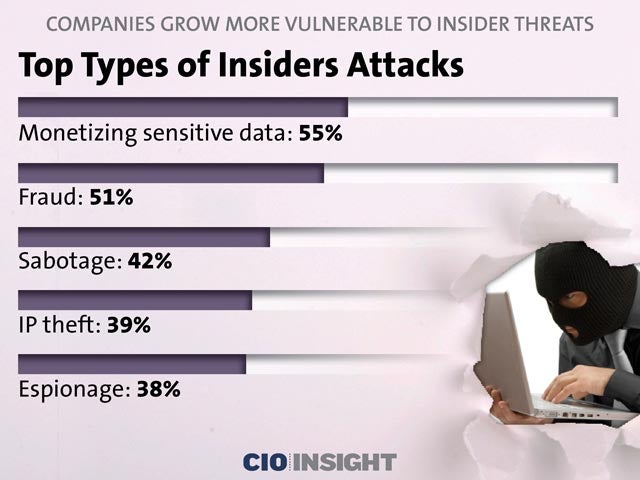 Top Types of Insiders Attacks
Top Types of Insiders Attacks
Monetizing sensitive data: 55%,
Fraud: 51%,
Sabotage: 42%,
IP theft: 39%,
Espionage: 38%
 The Most Vulnerable Assets
The Most Vulnerable Assets
Databases: 57%,
File servers: 55%,
Mobile devices: 44%,
Endpoints: 44%,
Business applications: 42%
 Customer Data Is Most Vulnerable
Customer Data Is Most Vulnerable
Customer data is most vulnerable to insider attacks at 63%. Financial data and intellectual property follow at 55% and 54%, respectively.
 Launch Points of Insider Attacks
Launch Points of Insider Attacks
Endpoints (57%) beat out mobile devices (36%), networks (35%) and cloud infrastructure (20%) as the most common assets used to launch insider attacks.
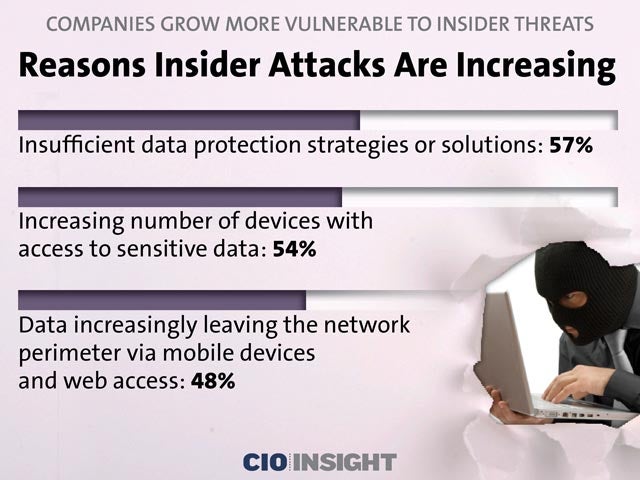 Reasons Insider Attacks Are Increasing
Reasons Insider Attacks Are Increasing
Insufficient data protection strategies or solutions: 57%,
Increasing number of devices with access to sensitive data: 54%,
Data increasingly leaving the network perimeter via mobile devices and web access: 48%
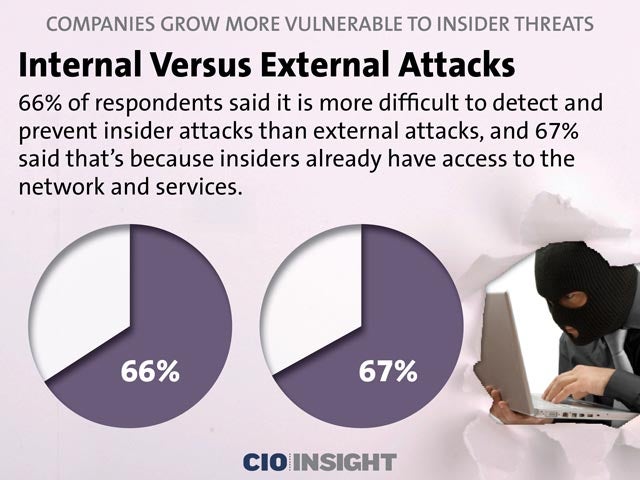 Internal Versus External Attacks
Internal Versus External Attacks
66% of respondents said it is more difficult to detect and prevent insider attacks than external attacks, and 67% said that’s because insiders already have access to the network and services.
 Insider Threat Analytics
Insider Threat Analytics
Asked whether their organization leverages analytics to determine insider threats, 56% said they do, 30% said they don’t and 14% are unsure.
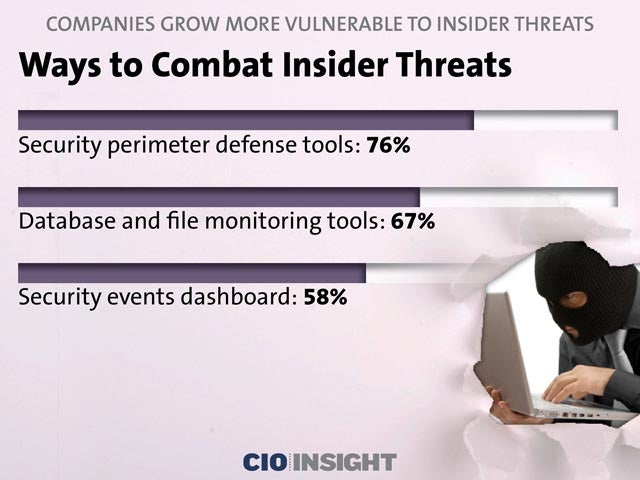 Ways to Combat Insider Threats
Ways to Combat Insider Threats
Security perimeter defense tools: 76%,
Database and file monitoring tools: 67%,
Security events dashboard: 58%
 Barriers to Managing Insider Threats
Barriers to Managing Insider Threats
Lack of training and expertise: 60%,
Lack of budget: 50%,
Lack of collaboration between departments: 48%













