The Return of the Malicious Attachment
 The Return of the Malicious Attachment
The Return of the Malicious Attachment
A new report finds that attachment-based cyber-warfare campaigns have returned in full force, in part because they are efficient and cost-effective.
 What Caused the Return of Malicious Macros?
What Caused the Return of Malicious Macros?
Malicious macro attachment campaigns have grown rapidly in size and frequency because they: Very successfully evade leading traditional signature- and reputation-based defenses; Evade “newer behavioral sandboxes”; Are easily and inexpensively frequently updated
 More Reasons for the Growth of Malicious Macros
More Reasons for the Growth of Malicious Macros
Malicious macros also appeal to hackers now because they: Are cross-platform and unpatchable. They are not limited by vulnerabilities in specific OSs or application versions; Rely on end-user interaction to bypass automated defenses; Have low upfront and maintenance costs, which increase the ROI
 URL-Based Campaign Changes
URL-Based Campaign Changes
Instead of relying on unsolicited email to rope in users, exploit kits such as Angler, RIG and Magnitude deliver CryptoWall and other ransomware to Web servers and compromise infected ad networks.
 Attackers Exploit Social Media
Attackers Exploit Social Media
Distributing malicious content via social media pays off for hackers and scammers. A single phishing lure, malware link or spam message may reach 10,000 or more potential victims.
 High-Profile Current Events Exploited
High-Profile Current Events Exploited
Cyber-attackers target branded social media destinations linked to popular events like NFL Playoffs/Super Bowl, Valentine’s Day, and March Madness. They plant malicious content and lures specifically designed to attract massive demographics these events attract.
 Fewer Unsolicited Messages
Fewer Unsolicited Messages
Overall, the amount of unsolicited messages declined in 2014 compared to 2013 because of high-profile botnet takedowns.
 Message Volume Declined but Malice Increased
Message Volume Declined but Malice IncreasedAlthough the decrease in message volume seems counterintuitive in light of late-2014 public record breaches, maliciousness made up for lost volume. Increased ransomware, other cyber-extortion techniques, and unsolicited email foiled anti-virus detection.
 Daily Unsolicited Message Volume
Daily Unsolicited Message Volume
Median daily volume of unsolicited messages dropped 30% from January to June of this year. The proportion of malicious URLs in these messages remained consistent, ranging from 10 to 20%, however.
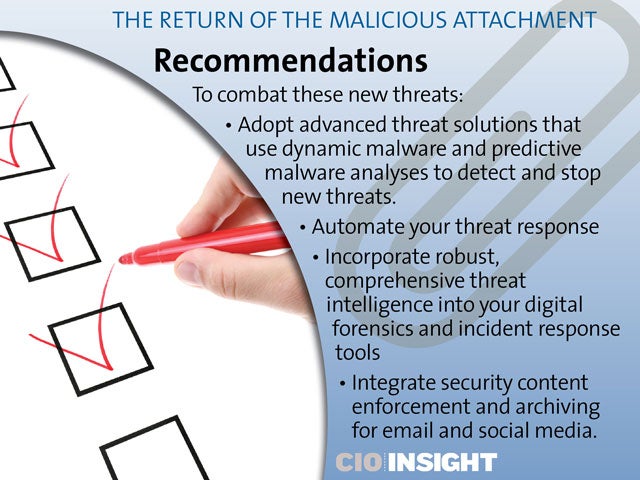 Recommendations
Recommendations
To combat these new threats: Adopt advanced threat solutions that use dynamic malware and predictive malware analyses to detect and stop new threats.; Automate your threat response; Incorporate robust, comprehensive threat intelligence into your digital forensics and incident response tools; Integrate security content enforcement and archiving for email and social media.













