White & Black Hats Point Out Security Blind Spots
 White & Black Hats Point Out Security Blind Spots
White & Black Hats Point Out Security Blind Spots
Both well-meaning and malicious hackers fess up to why they hack, and list the best data exfiltration strategies and the least effective security tools.
 Black Hat Versus White Hat
Black Hat Versus White Hat
81% of survey respondents had worked in corporate IT in the past. Respondents were almost evenly split between white hats (52%) and black hats or other (48%).
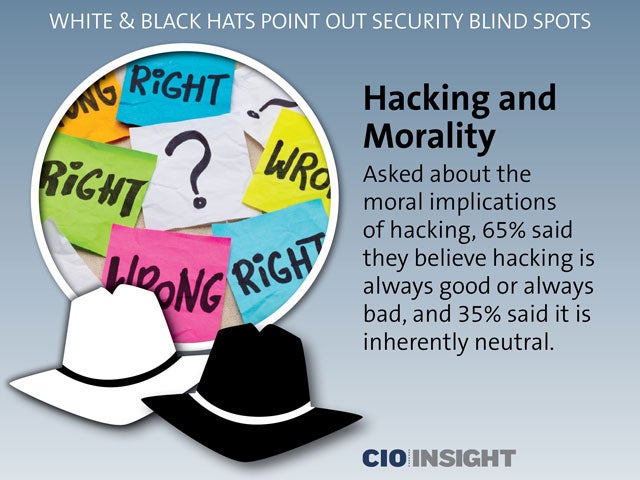 Hacking and Morality
Hacking and Morality
Asked about the moral implications of hacking, 65% said they believe hacking is always good or always bad, and 35% said it is inherently neutral.
 Motivation for Hacking
Motivation for Hacking
Stealing data can be very lucrative, as evidenced by the fact that some white hat hackers leave their IT jobs to become black hats. 83% said money is the primary motivation for hacking.
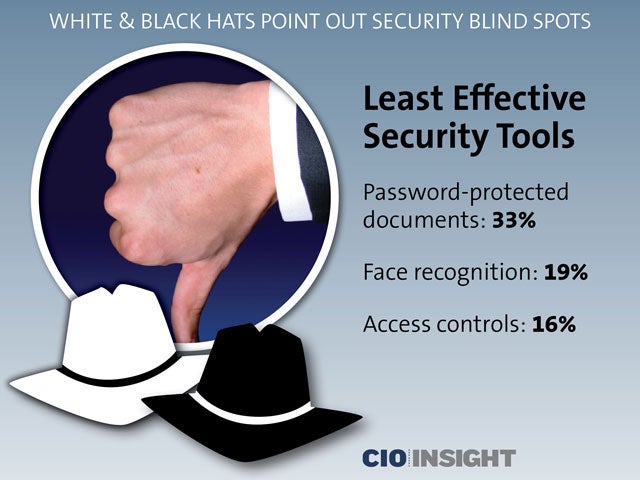 Least Effective Security Tools
Least Effective Security Tools
Password-protected documents: 33%,
Face recognition: 19%,
Access controls: 16%
 Top Data Exfiltration Methods
Top Data Exfiltration Methods
Phishing: 59%,
Malware: 26%,
Physical theft: 6%,
WiFi spoofing: 5%,
Other: 4%
 Biggest Blind Spots
Biggest Blind Spots
61% of the experts surveyed identified unmanaged devices as a critical security blind spot. Systems that are not up to date followed at 55%, and 36% named mobile devices as the third major blind spot.
 Need for Tools
Need for Tools
These security vulnerabilities demonstrate the need for tools—such as cloud access security brokers—that maintain comprehensive, real-time visibility and control over data.
 Recommendation
Recommendation
Organizations should adopt real-time security solutions with comprehensive data protection across all devices and applications.