A Lack of Integration Hampers Threat Detection
 A Lack of Integration Hampers Threat Detection
A Lack of Integration Hampers Threat Detection
Lack of automation integration and workflow between security and response are hindering organizations’ ability to prevent, detect and respond to cyber-threats.
 Security Efforts Often Done Manually
Security Efforts Often Done Manually
39% of the security pros surveyed collect and store data and perform analyses mostly or completely manually, and 42% said they are equally manual and automated.
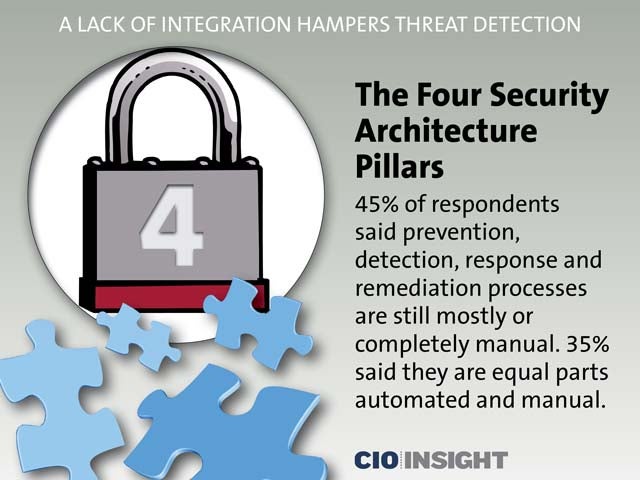 The Four Security Architecture Pillars
The Four Security Architecture Pillars
45% of respondents said prevention, detection, response and remediation processes are still mostly or completely manual. 35% said they equal parts automated and manual.
 Tools Deployed
Tools Deployed
There is more deployment of tools in the proactive areas of prevention and detection, and less implementation of tools in the reactive areas of response and remediation.
 Securities Tools and Services Deployed
Securities Tools and Services Deployed
Anti-malware, Antivirus: protect/prevent (90%), detect (80%), respond/remediate (59%).
Endpoint Security: protect/prevent (79%), detect (71%) respond/remediate (44%).
IDS/IPS/UTM: protect/prevent (70%), detect (75%), respond/remediate (36%).
Vulnerability Management: protect/prevent: (59%), detect (65%), respond/remediate (39%).
Web Security: protect/prevent (70%), detect (38%), response/remediate (25%)
 Endpoint Systems Protected
Endpoint Systems Protected
92% of respondents said their tools cover server endpoints, 86% reported that they cover company-owned devices, and 79% said cover their web-facing applications.
 Centralizing Security Data
Centralizing Security Data
Organizations that want to integrate and automate security processes should centralize—or at least provide appropriate access to—security-related data. But responses indicate that 54% are not centralizing this data.
 Centralizing Security Data (Continued)
Centralizing Security Data (Continued)
Of the 37% who do centralize prevention, detection, response and remediation data, 79% do so in a Security Incident and Event Manager (SIEM), 25% use the cloud and 24% use other analytics systems.
 Who Can Access Centralized Security Data?
Who Can Access Centralized Security Data?
Security analysts: 69%,
Responders: 63%,
Administrators: 61%,
Operational IT groups: 57%
 Impediments to Integration
Impediments to Integration
The top two impediments to the full visibility needed to prevent, detect, respond to and remediate security events on networks are the lack of skills and staffing (84%) and the lack of funding and management buy-in (56%).
 Lack Of Interoperability
Lack Of Interoperability
The third inhibitor is the lack of workflow among the four pillars (34% of respondents), pointing to a lack of interoperability.
 Steps to Success
Steps to Success
The key to success is high-level management buy-in, regardless of tools or process. Once leadership and vision come from a common source, organizations can align the goals of each security function, and then use teams, processes and tools to automate and further integrate.













