How Downtime Impedes Digital Transformations
 How Downtime Impedes Digital Transformations
How Downtime Impedes Digital Transformations
Unplanned downtime and other availability and protection gaps are costing organizations millions a year and can stall companies’ digital transformation efforts.
 Road Block
Road Block
66% of the IT decision-makers surveyed said their digital transformation initiatives are being inhibited due to unplanned downtime.
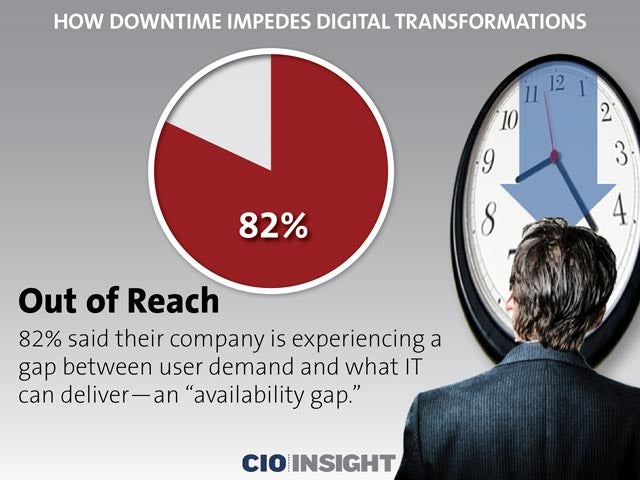 Out of Reach
Out of Reach
82% said their company is experiencing a gap between user demand and what IT can deliver—an “availability gap.”
 Vulnerable Position
Vulnerable Position
72% of the IT decision-makers surveyed said their organization is experiencing a “protection gap”—IT’s inability to protect data often enough to satisfy user tolerance.
 Huge Expense
Huge Expense
The availability and protection gaps cost organizations an average of $21.8 million a year—up from $10 million in 2015.
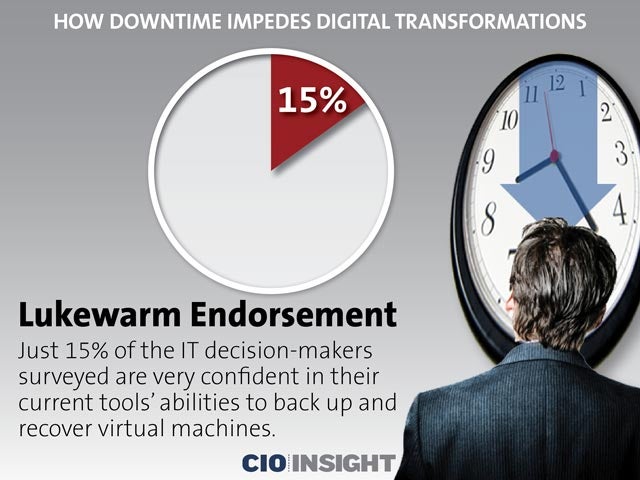 Lukewarm Endorsement
Lukewarm Endorsement
Just 15% of the IT decision-makers surveyed are very confident in their current tools’ abilities to back up and recover virtual machines.
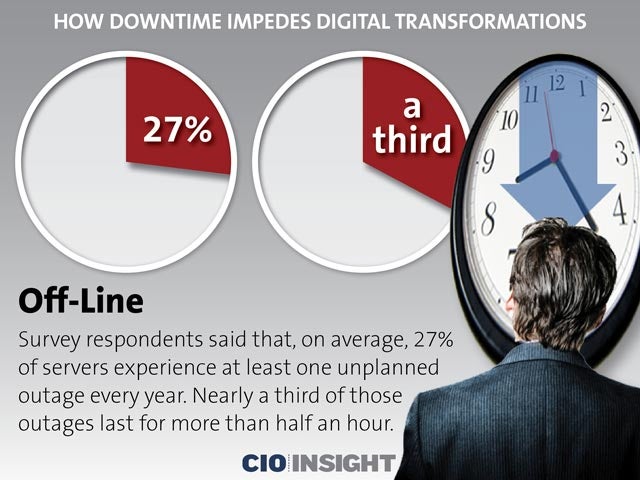 Off-Line
Off-Line
Survey respondents said that, on average, 27% of servers experience at least one unplanned outage every year. Nearly a third of those outages last for more than half an hour.
 Stringent Standards
Stringent Standards55% said that no more than 15 minutes of downtime is tolerable for high-priority apps, but 22% said that no amount of downtime is acceptable for these apps.
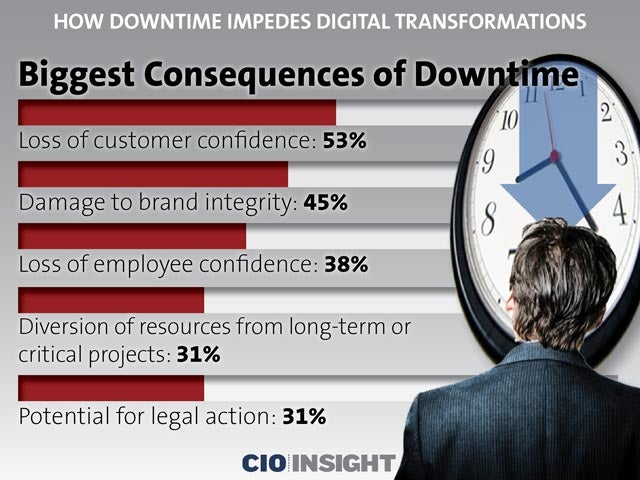 Biggest Consequences of Downtime
Biggest Consequences of Downtime
Loss of customer confidence: 53%,
Damage to brand integrity: 45%,
Loss of employee confidence: 38%,
Diversion of resources from long-term or critical projects: 31%,
Potential for legal action: 31%
 Top Cloud-Based Services in Use
Top Cloud-Based Services in Use
Software as a Service: 39%,
Infrastructure as a Service: 31%,
Platform as a Service: 28%













