Phishing Prevails Despite Investments in Security
 Phishing Prevails Despite Investments in Security
Phishing Prevails Despite Investments in Security
Despite layered security at most organizations, phishing attacks continue, but trained workers are good at detecting attacks such as business email compromises.
 Phishing Continues
Phishing Continues
66% of the senior IT decision-makers surveyed said their company has experienced a phishing-related incident, and most still worry about email-related threats.
 Suspicious Emails Reported Weekly
Suspicious Emails Reported Weekly
1 to 50 emails: 36%,
51 to 100 emails: 17%,
101 to 500 emails: 17%,
501 to 1,000 emails: 10%,
1,000 or more emails: 21%
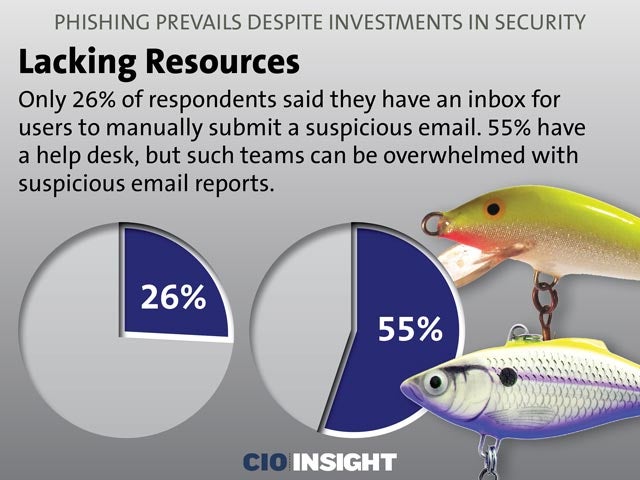 Lacking Resources
Lacking Resources
Only 26% of respondents said they have an inbox for users to manually submit a suspicious email. 55% have a help desk, but such teams can be overwhelmed with suspicious email reports.
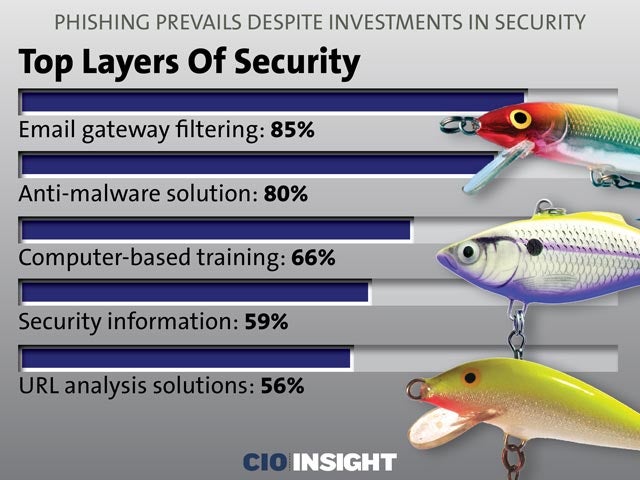 Top Layers Of Security
Top Layers Of Security
Email gateway filtering: 85%,
Anti-malware solution: 80%,
Computer-based training: 66%,
Security information: 59%,
URL analysis solutions: 56%
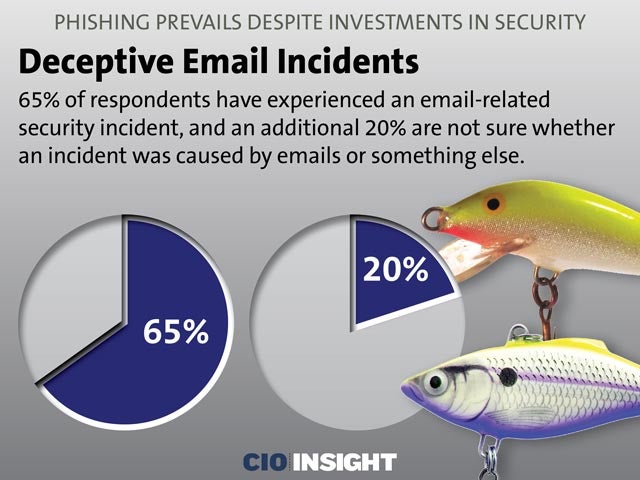 Deceptive Email Incidents
Deceptive Email Incidents
65% of respondents have experienced an email-related security incident, and an additional 20% are not sure whether an incident was caused by emails or something else.
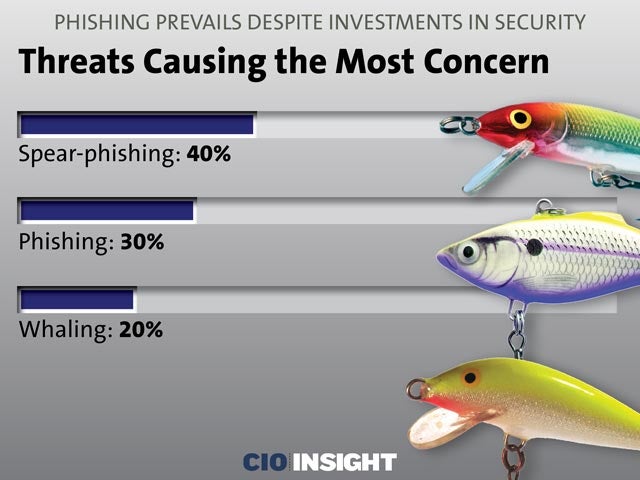 Threats Causing the Most Concern
Threats Causing the Most Concern
Spear-phishing: 40%
Phishing: 30%
Whaling: 20%
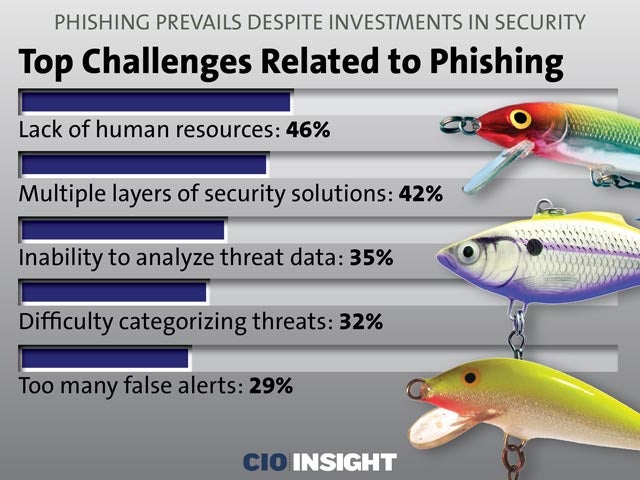 Top Challenges Related to Phishing
Top Challenges Related to Phishing
Lack of human resources: 46%
Multiple layers of security solutions: 42%
Inability to analyze threat data: 35%
Difficulty categorizing threats: 32%
Too many false alerts: 29%
 Feeling Insecure
Feeling Insecure43% of respondents said their responses to phishing range from “totally ineffective” to “mediocre.”
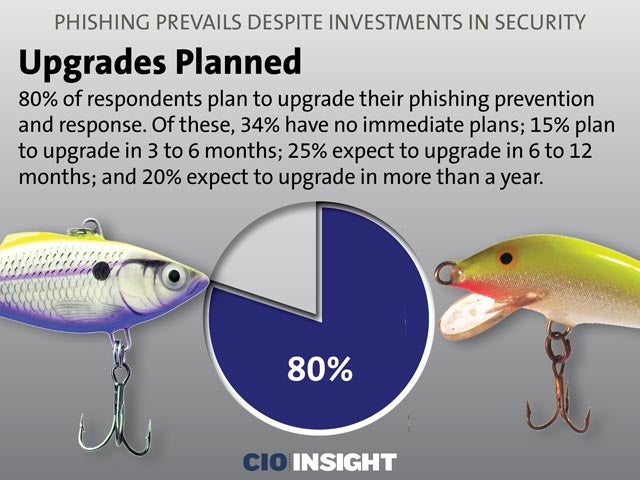 Upgrades Planned
Upgrades Planned
80% of respondents plan to upgrade their phishing prevention and response. Of these, 34% have no immediate plans; 15% plan to upgrade in 3 to 6 months; 25% expect to upgrade in 6 to 12 months; and 20% expect to upgrade in more than a year.
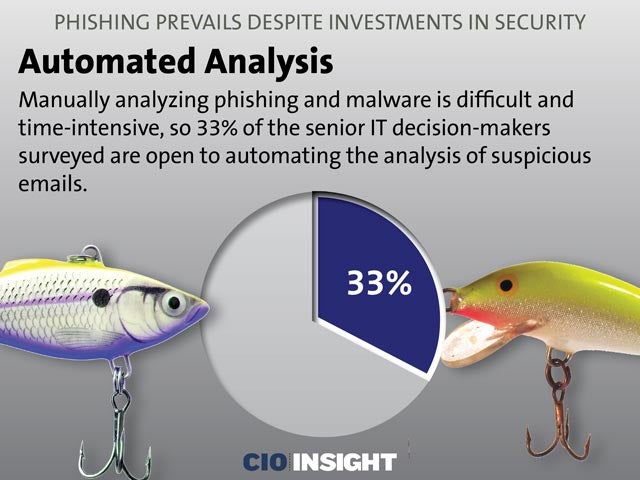 Automated Analysis
Automated Analysis
Manually analyzing phishing and malware is difficult and time-intensive, so 33% of the senior IT decision-makers surveyed are open to automating the analysis of suspicious emails.













